Software de Monitoramento de Rede: OpMon Traffic Analyzer

Para que o OpMon Traffic Analyzer possa funcionar corretamente é necessário que exista em sua rede um dispositivo que possua suporte ao protocolo Netflow. O protocolo Netflow é encarregado de coletar as informações sobre o tráfego da rede e enviá-las para que o OpMon Traffic Analyzer possa gerar as informações de forma consolidada.
Diante da necessidade de protocolos que ofereçam informações do tráfego de uma rede de grande porte com baixo custo computacional, o IETF propôs a criação do padrão IPFIX (IP Flow Information Export), cuja finalidade era estabelecer uma arquitetura para análise de tráfego. Subsequentemente a este trabalho, diversos protocolos foram propostos, dentre eles o Netflow (RFC 3954), criado pela Cisco Systems. O grupo de trabalho escolheu o Netflow como protocolo a ser desenvolvido e implementado.
Principais vantagens de utilização do Netflow
- Funcionamento como cache para acelerar os lookups nas tabelas de roteamento;
- Dispensa a verificação de tabelas de access-list (apenas de entrada) toda vez que um pacote chega, ficando mais eficiente o processo de roteamento;
- Permite a exportação das informações de fluxo utilizadas pelo cache do Netflow, facilitando a coleta de dados para futuras análises sem a necessidade de colocar um analisador em cada enlace.
A Cisco define um fluxo como uma sequência unidirecional de pacotes entre máquinas de origem e destino e, pode se dizer que o Netflow provê a sumarização de informações sobre o tráfego de um roteador ou switch. Fluxos de rede são altamente granulares e identificados por ambos os endereços IP e pelo número das portas da camada de transporte. O Netflow também utiliza, para identificar unicamente um fluxo, os campos “Protocol type” e “Type of Service” (ToS) do IP e a interface lógica de entrada do roteador ou switch.
Os fluxos mantidos no cache do roteador/switch são exportados para um coletor (OpMon Traffic Analyzer) nas seguintes situações: o elemento permanece ocioso por mais de 15 segundos, sua duração excede 30 minutos, uma conexão TCP é encerrada com a flag “FIN” ou “RST”, a tabela de fluxos está cheia ou o usuário redefine as configurações de fluxo. O tempo máximo que um fluxo permanece no dispositivo antes de ser exportado é de 30 minutos.
Para que o Netflow funcione em um roteador ou switch é necessário que a versão do seu sistema operacional possua suporte e este protocolo. Recomendamos que você consulte seu fornecedor de redes sobre quais equipamentos possuem este suporte.
Nos roteadores Cisco, por exemplo, não existe um comando geral que habilite o Netflow para todas as interfaces e, para sua habilitação, é necessária a habilitação individual por interface, através do comando route-cache flow. O processo de Netflow funciona apenas para os pacotes de entrada, logo os pacotes exportados pelo Netflow dizem respeito apenas ao tráfego entrante na interface habilitada.
Para o Netflow, o fluxo é definido como sendo um conjunto de cinco variáveis, além do “Protocol Type”: IP origem, IP destino, porta origem e porta destino. Além destas variáveis, as tabelas do Netflow guardam a interface origem e a de destino, relativas ao trânsito do pacote IP.
A cada pacote IP entrante na interface, o Netflow identifica o seu fluxo e verifica se já existe uma entrada deste fluxo na tabela de cache. Se existir, ele comuta diretamente para a interface de destino especificada e, se não, realizará um lookup nas tabelas de roteamento e nas tabelas de access-list. Se este pacote possuir alguma restrição nas tabelas de access-list ou se o seu IP destino não for achado nas tabelas de roteamento o pacote então será enviado para a interface “NULL” (um pacote com o destino para esta interface identifica ele foi descartado). O Netflow também cria uma entrada na sua tabela de cache para o destino “NULL”.
Outro processo importante no Netflow é o de exportação dos dados, conhecido como flow-export. O flow-export é realizado através do envio de dados encapsulados em pacotes UDP. Seu destino é o IP do OpMon Traffic Analyzer previamente no roteador e, o conteúdo do pacote UDP dependerá da versão do Netflow. Atualmente os roteadores podem exportar os fluxos criados pelo Netflow nas versões de 1 a 8. O momento pelo qual o roteador começa a exportar os dados de fluxo dependerá da configuração.
Na prática, o Netflow é um software para caracterizar a operação da rede, sendo fundamental para mapear o comportamento da rede, incluindo: aplicação e uso, eficiência e utilização dos recursos, impacto de mudanças e alterações, anormalidades e vulnerabilidades. O Netflow cria um ambiente com ferramentas para compreender “quem”, “o que”, “quando” e “como” o tráfego flui pela rede, permitindo melhorias nos processos e adequações do ambiente às necessidades de negócio.
Tradicionalmente, o mercado confia no monitoramento de largura de banda baseado no SNMP que. embora facilite o planejamento de capacidade, faz pouco para caracterizar padrões de tráfego e aplicações, essenciais para compreender o “quanto” e “como” a rede pode suportar o negócio. Um entendimento mais detalhado de como a banda está sendo usada é extremamente importante em redes IP; contadores de pacotes e bytes de interface são úteis, mas entender quais os endereços IP são origem e destino do tráfego e quais aplicações o estão gerando, é incalculável.
A capacidade de caracterizar o tráfego IP e entender “onde” e “como” ele flui é fundamental para o desempenho da rede, disponibilidade e solução de problemas. O monitoramento dos fluxos de tráfego IP facilita o planejamento de capacidade e assegura que os recursos sejam utilizados de forma adequada e em apoio às metas organizacionais. Ela ajuda a determinar onde aplicar o QoS, otimizar o uso de recursos e desempenha um papel vital na segurança da rede ao detectar ataques de negação de serviço (DoS), propagação de worms e outros eventos indesejáveis na rede.
O Netflow soluciona muitos problemas comuns encontrados pelos profissionais de TI e telecomunicações, como:
- Analisar novas aplicações e seu impacto rede – identificar as cargas das novas aplicações na rede, como SAP ou inclusão de novos sites remotos;
- Redução do pico de tráfego WAN – avaliar o impacto na rede com a aplicação de novas políticas, identificar “quem” está utilizando a rede e os “top talkers”;
- Solução de problemas e identificação de gargalos e pontos críticos da rede – diagnosticar quedas de desempenho na rede (lentidão);
- Detecção de tráfego não autorizado – evita atualizações caras, identificando as aplicações que estão causando congestionamento;
- Segurança e detecção de anomalias;
- Validação dos parâmetros de QoS – alocação de largura de banda adequada para cada classe de serviço (CoS).
Cada pacote transmitido por um roteador ou switch é examinado por um conjunto de atributos do pacote IP, que são a identidade do pacote IP ou a impressão digital do pacote e determinam se o pacote é único ou similar a outros pacotes.
Todos os pacotes com o mesmo IP de origem/destino, portas de origem/destino, interface de protocolo e classe de serviço são agrupados em um fluxo de pacotes e bytes, e então são contados e condensados em um banco de dados chamado sw cache Netflow. A figura a seguir ilustra este processo.
As informações de fluxo são extremamente úteis para a compreensão do comportamento da rede:
- Endereço de origem: informa a origem do tráfego;
- Endereço de destino: diz quem está recebendo o tráfego;
- Portas: caracterizam a aplicação;
- Classe de serviço: examina a prioridade do tráfego;
- Interface: conta como tráfego está sendo utilizado pelo dispositivo de rede.
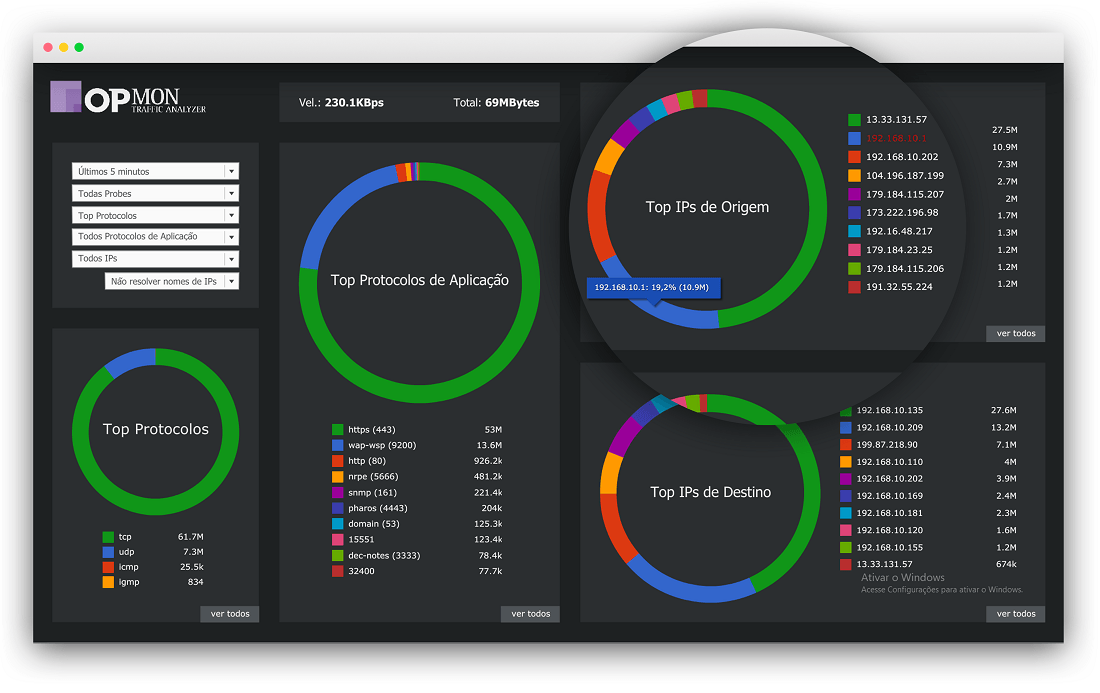
O Netflow deve ser “exportado” para um servidor de relatórios, também conhecido como “coletor Netflow”, em nosso caso, o OpMon Traffic Analyzer. O OpMon Traffic Analyzer organiza, interpreta os fluxos exportados e os combina para gerar relatórios úteis para a análise de tráfego e de segurança. O Netflow, ao contrário do polling SNMP, exporta as informações periodicamente para o coletor.
Um fluxo está pronto a para exportação, quando estiver inativo por certo tempo (sem novos pacotes recebidos), ou se o fluxo é de longa vida (ativo) e tem uma duração maior do que o timer ativo (FTP de arquivos grandes). Além disso, o fluxo está pronto para exportação, quando um flag TCP indicar o fluxo terminou. Há temporizadores (timers) para determinar se um fluxo está inativo ou se é um fluxo de longa duração. Todos os timers para exportação são configuráveis, mas os padrões são usados na maioria dos casos. O coletor pode combinar os fluxos e agregar tráfego. Por exemplo, um FTP que dure mais do que o timer ativo pode ser dividido em múltiplos fluxos e o coletor pode combiná-los mostrando o total do tráfego FTP para um servidor em um momento específico do dia.
